Search Results
Showing results 1 to 6 of 6

Public Key Encryption: Kid Krypto
Source Institutions
In this activity, learners conduct a simulation exercise related to public key encryption and try to intercept a message sent between two learners.

Programming Languages: Marching Orders
Source Institutions
In this activity about computer programming, learners follow instructions in a variety of ways in order to successfully draw figures.
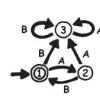
Treasure Hunt: Finite-State Automata
In this computer science activity about finite-state automaton (on page 45 of the PDF), learners use a map and choose various pathways to find Treasure Island.
Sound Representation: Modems Unplugged
Source Institutions
In this activity, learners listen to songs and decode hidden messages based on the same principle as a modem. As a final challenge, learners decode the binary messages in a music video.

The Muddy City: Minimal Spanning Trees
Source Institutions
In this puzzle, learners investigate the decisions involved in linking a network between houses in a muddy city.

Cryptographic Protocols: The Peruvian Coin Flip
Source Institutions
This activity about cryptographic techniques illustrates how to accomplish a simple, but nevertheless seemingly impossible task—making a fair, random choice by flipping a coin between two people who d
