Search Results
Showing results 1 to 11 of 11

Public Key Encryption: Kid Krypto
Source Institutions
In this activity, learners conduct a simulation exercise related to public key encryption and try to intercept a message sent between two learners.

Battleships: Searching Algorithms
Source Institutions
This activity explores the main algorithms that are used as the basis for searching on computers, using different variations on the game of battleships.
Divide and Conquer: Santa's Dirty Socks
Source Institutions
This activity introduces the idea of "divide and conquer" using a fictitious but serious problem--a pair of dirty socks has accidentally been wrapped in one of the presents that Santa is about to deli
Solving Playground Network Problems
Source Institutions
In this activity, learners use cooperation and logical thinking to find solutions to network problems on the playground.
Sound Representation: Modems Unplugged
Source Institutions
In this activity, learners listen to songs and decode hidden messages based on the same principle as a modem. As a final challenge, learners decode the binary messages in a music video.

Arduino Blink Challenge
Source Institutions
In this activity, learners explore computer programming and the impact of computers on society. Learners build and test a program to turn a light on and off using an Arduino board.

The Muddy City: Minimal Spanning Trees
Source Institutions
In this puzzle, learners investigate the decisions involved in linking a network between houses in a muddy city.

Cryptographic Protocols: The Peruvian Coin Flip
Source Institutions
This activity about cryptographic techniques illustrates how to accomplish a simple, but nevertheless seemingly impossible task—making a fair, random choice by flipping a coin between two people who d

The Orange Game: Routing and Deadlock in Networks
Source Institutions
When a lot of people share one network (such as cars using roads, or messages getting through the Internet), there is the possibility that competing processes will create a “deadlock," or an interrupt

Information Hiding: Sharing Secrets
Source Institutions
This activity about cryptographic techniques illustrates a situation where information is shared, and yet none of it is revealed.
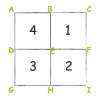
Beat the Clock: Sorting Networks
Source Institutions
Even fast computers are limited to how quickly they can solve problems. One way to speed things up is to use several computers at once.
