Search Results
Showing results 1 to 20 of 43

Public Key Encryption: Kid Krypto
Source Institutions
In this activity, learners conduct a simulation exercise related to public key encryption and try to intercept a message sent between two learners.

Battleships: Searching Algorithms
Source Institutions
This activity explores the main algorithms that are used as the basis for searching on computers, using different variations on the game of battleships.

Twenty Guesses: Information Theory
Source Institutions
This activity introduces the idea that computer scientists measure information by how "surprising" a message is.
Space Weather Action Center
Source Institutions
In this interdisciplinary activity, learners create a Space Weather Action Center (SWAC) to monitor solar storms and develop real SWAC news reports.

The Poor Cartographer: Graph Coloring
Source Institutions
In this activity, learners help a poor cartographer color in the countries on a map, making sure each country is colored a different color than any of its neighbors.

Pico Cricket Compass
Source Institutions
Learners can program a compass to draw a circle by itself using a Pico Cricket, some Legos, and lots of tape! Pico Cricket is required.
Divide and Conquer: Santa's Dirty Socks
Source Institutions
This activity introduces the idea of "divide and conquer" using a fictitious but serious problem--a pair of dirty socks has accidentally been wrapped in one of the presents that Santa is about to deli

Programming Languages: Marching Orders
Source Institutions
In this activity about computer programming, learners follow instructions in a variety of ways in order to successfully draw figures.

LEGO Orrery
Source Institutions
Use this model to demonstrate the goal of NASA's Kepler Mission: to find extrasolar planets through the transit method.
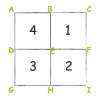
Colour by Numbers: Image Representation
Source Institutions
This activity shows learners how computers use numbers to represent pictures. A grid is used to represent the pixels (short for picture elements) of a computer screen.
Treasure Hunt: Finite-State Automata
In this computer science activity about finite-state automaton (on page 45 of the PDF), learners use a map and choose various pathways to find Treasure Island.
Solving Playground Network Problems
Source Institutions
In this activity, learners use cooperation and logical thinking to find solutions to network problems on the playground.

Passion for Pixels
Source Institutions
In this technology activity, learners explore digital imaging and pixels. Learners "transmit" an image to a partner by creating an image on grid paper.
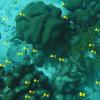
Coral Snapshots: Biodiversity in Marine Protected Areas
Source Institutions
In this data activity, learners analyze data from coral reef snapshots taken by scientists at the Virginia Institute of Marine Science.

You Can Say That Again!: Text Compression
Source Institutions
This activity helps students learn how computers "compress" text by identifying repeating patterns of letters, words, and phrases.
Sound Representation: Modems Unplugged
Source Institutions
In this activity, learners listen to songs and decode hidden messages based on the same principle as a modem. As a final challenge, learners decode the binary messages in a music video.

Locating a Point
Source Institutions
In this activity, learners work in teams to simulate the process used by Global Positioning Systems (GPS) to determine the location of a fallen meteorite in Antarctica.

EEEEK--A Mouse!
Source Institutions
In this activity, learners explore the concept of how engineering solved the problem of human/computer interface.

Binary Code Bracelets
Source Institutions
In this activity, learners make their own binary code bracelets by translating their initials into 0s and 1s represented by beads of 2 different colors.

Card Flip Magic: Error Detection & Correction
Source Institutions
This magic trick is based on how computers detect and correct data errors.
