Search Results
Showing results 1 to 18 of 18

Public Key Encryption: Kid Krypto
Source Institutions
In this activity, learners conduct a simulation exercise related to public key encryption and try to intercept a message sent between two learners.

Battleships: Searching Algorithms
Source Institutions
This activity explores the main algorithms that are used as the basis for searching on computers, using different variations on the game of battleships.
Count the Dots: Binary Numbers
Source Institutions
Data in computers is stored and transmitted as a series of zeros and ones. Learners explore how to represent numbers using just these two symbols, through a binary system of cards.

Color by Numbers: Image Representation
Source Institutions
Computers store drawings, photographs, and other pictures using only numbers. Through this activity, learners decode numbers to create pictures using the same process that computers use.
Divide and Conquer: Santa's Dirty Socks
Source Institutions
This activity introduces the idea of "divide and conquer" using a fictitious but serious problem--a pair of dirty socks has accidentally been wrapped in one of the presents that Santa is about to deli
Lightest and Heaviest: Sorting Algorithms
Source Institutions
Computers are often used to put lists into some sort of order—for example, names into alphabetical order, appointments or e-mail by date, or items in numerical order.

Programming Languages: Marching Orders
Source Institutions
In this activity about computer programming, learners follow instructions in a variety of ways in order to successfully draw figures.
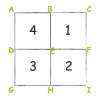
Colour by Numbers: Image Representation
Source Institutions
This activity shows learners how computers use numbers to represent pictures. A grid is used to represent the pixels (short for picture elements) of a computer screen.
Treasure Hunt: Finite-State Automata
In this computer science activity about finite-state automaton (on page 45 of the PDF), learners use a map and choose various pathways to find Treasure Island.
Solving Playground Network Problems
Source Institutions
In this activity, learners use cooperation and logical thinking to find solutions to network problems on the playground.
Sound Representation: Modems Unplugged
Source Institutions
In this activity, learners listen to songs and decode hidden messages based on the same principle as a modem. As a final challenge, learners decode the binary messages in a music video.

Arduino Blink Challenge
Source Institutions
In this activity, learners explore computer programming and the impact of computers on society. Learners build and test a program to turn a light on and off using an Arduino board.

Binary Challenge
Source Institutions
In this activity, learners cut out 5 paper cards and label them with 1, 2, 4, 8, or 16 dot(s) to explore binary digits.

The Muddy City: Minimal Spanning Trees
Source Institutions
In this puzzle, learners investigate the decisions involved in linking a network between houses in a muddy city.

Cryptographic Protocols: The Peruvian Coin Flip
Source Institutions
This activity about cryptographic techniques illustrates how to accomplish a simple, but nevertheless seemingly impossible task—making a fair, random choice by flipping a coin between two people who d

The Orange Game: Routing and Deadlock in Networks
Source Institutions
When a lot of people share one network (such as cars using roads, or messages getting through the Internet), there is the possibility that competing processes will create a “deadlock," or an interrupt

Information Hiding: Sharing Secrets
Source Institutions
This activity about cryptographic techniques illustrates a situation where information is shared, and yet none of it is revealed.
Beat the Clock: Sorting Networks
Source Institutions
Even fast computers are limited to how quickly they can solve problems. One way to speed things up is to use several computers at once.
